Cybersecurity for industry
Three pillars of protection
Our integrated approach combines cutting-edge technologies to provide end-to-end security for your industrial digital assets.
Secure the communication
Industrial-level secure remote access, with plug-and-play simplicity for distributed infrastructures.
Secure execution
Real-time protection and firmware analysis based on AI for embedded systems and IoT devices.
Secure the destruction
Destruction of secured and certified data, ensuring the complete elimination of sensitive information on all storage media.
Secure connection
Tosi VPN to secure your communications
A secure industrial-grade remote access, as simple as plugging in a USB key. Connect your distributed infrastructure with military-grade encryption, without any configuration complexity.
Encryption & security
AES-256, Zero-trust architecture, no open inbound ports
Plug-and-play installation
No IT expertise required, the hardware and software are integrated
Global Connectivity
Connect your devices anywhere in the world
OT/IT Convergence
Link OT and IT networks with SSO, APIs, role-based access
Embedded security
Exein to secure execution
AI-driven security solutions for embedded systems and connected objects (IoT). Protect your firmware from the inside out.

Firmware Analysis
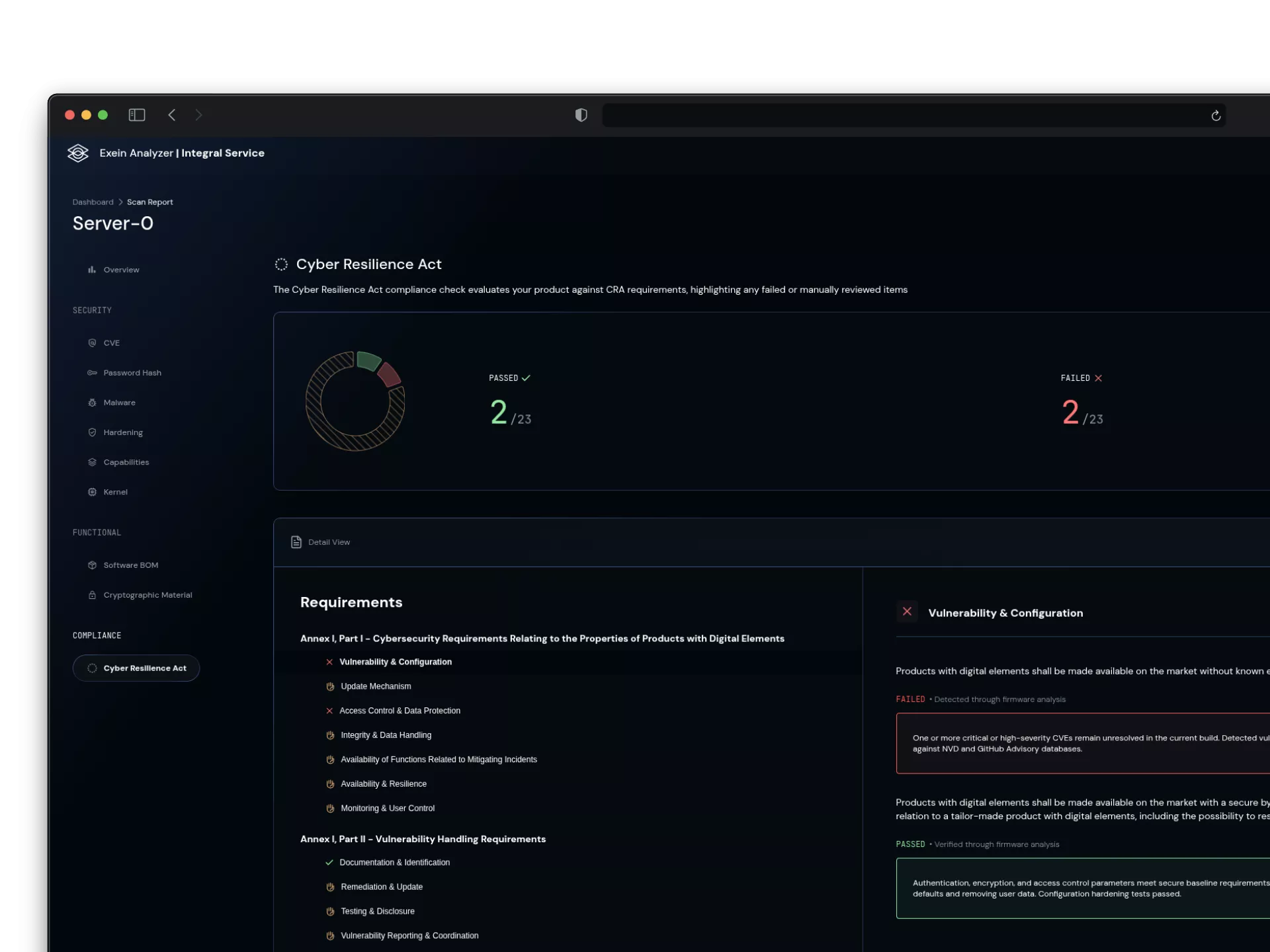
Exein Analyzer
On-demand firmware analysis platform that allows for the detection of vulnerabilities, identification of components, and providing actionable security insights.
Vulnerability detection
CVE & Zero-day
Detailed analysis
Firmware analysis
Binary analysis
reverse engineering
SBOM generation
For a more detailed analysis

Real-time protection
Exein Runtime
Light agent executing directly on embedded systems, ensuring continuous monitoring and immediate response to threats without impacting performance.
Real time monitoring
Ongoing threat detection
AI analysis
Detect threat by machine learning analysis
Zero-day protection
Real time protection against Zero days
Small footprint
Low performance impact
Secure destruction
Digital Data Destruction Service

When data needs to be deleted, it must be done permanently. Our certified destruction services guarantee a complete and irreversible elimination of sensitive information, in order to protect your organization against data breaches and compliance risks.
- For all types of media
- ISO 21964 and NAID certified
- Certificate of destruction
- Recycling included
Use Cases
End-of-life management of IT equipment
Data center dismantling
Regulatory compliance requirements
Data cleaning during mergers and acquisitions
Our teams at your service
We are here to help you as best as we can! Feel free to contact us via our form, by email, or directly by phone.